9 Ways to Secure Your Smartphone and Protect Your Mobile Privacy
Since the the revelations of Edward Snowden, we’ve all become a bit more paranoid about digital security and privacy. Snowden himself hasn’t owned a smartphone since he blew the whistle on the NSA’s illegal tracking actions in 2014 for fear of being tracked. Still, as Joseph Heller wrote in Catch-22, “just because you’re paranoid doesn’t mean they aren’t after you”.
To that length, Snowden has now partnered with hardware hacker Andrew “Bunnie” Huang to build a case for your iPhone 6. Once installed, it will alert you if the phone is broadcasting when it shouldn’t. The primary purpose is to protect journalists who are reporting in dangerous parts of the world like Marie Colvin who, in 2012, was killed by artillery fire. The Syrian military has been accused by Colvin’s family of targeting her using her mobile device.
Snowden’s device is not yet on the market, but there are still ways out there that make it easier to protect yourself and your phone from snooping.
1. Hardware Level Encryption

iOS has long supported hardware level encryption, and every new version seems to support more features. Android encrypts your storage by default ever since version 5.0 Marshmallow. In both cases they encrypt your data and can only be unlocked by the hardware in your phone.
However, it’s only as strong as your key. Setting up a lock code more complex than ‘1234’ or your birthday is one of the best security devices you can have.
2. Biometric scanning hardware
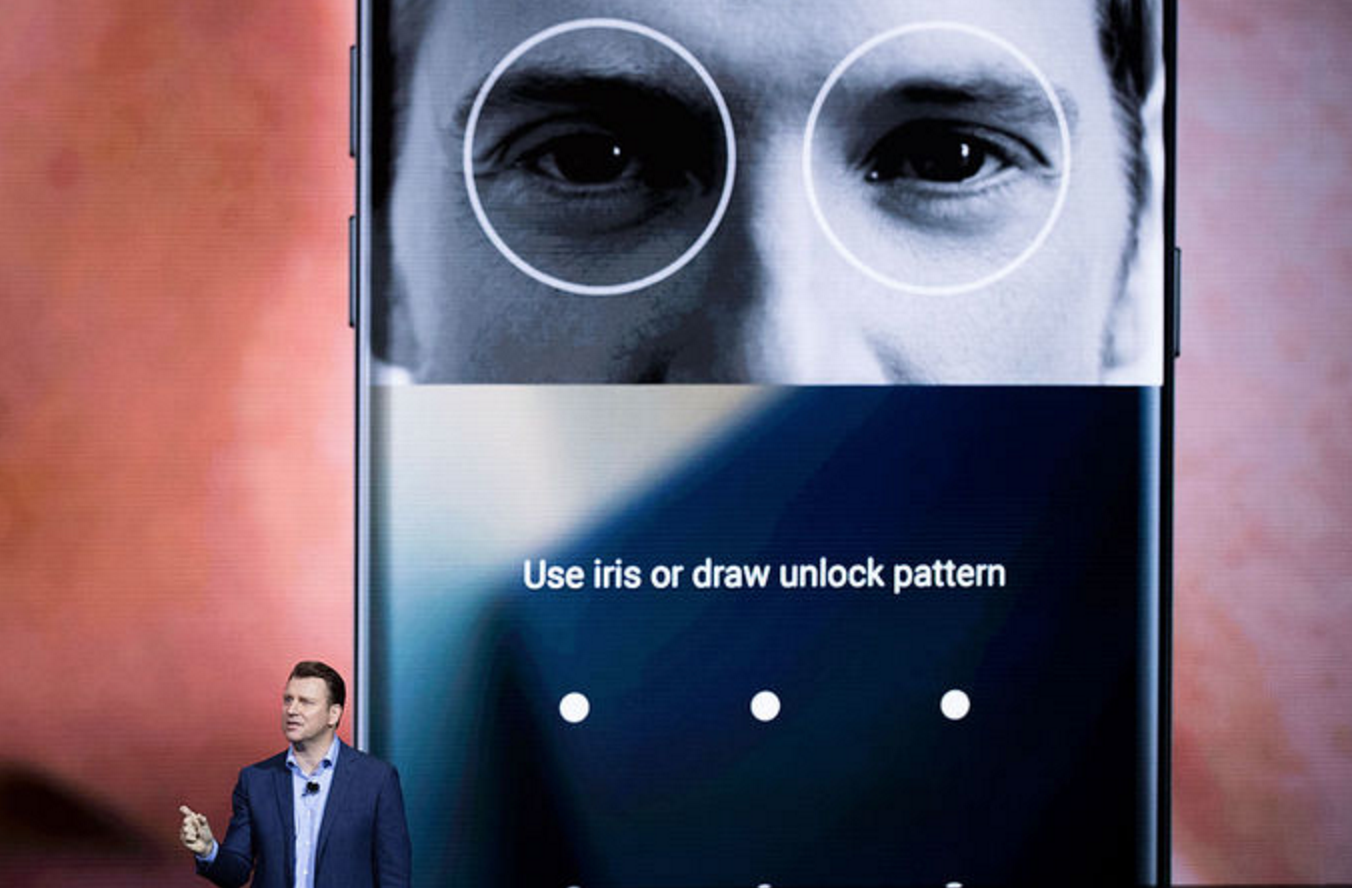
Why have passwords and codes to unlock your phone when fingerprint readers are on the newest iPhones and flagship Android phones? Securely unlocking your device is as quick as pressing a button. Iris scanners are the new biometric scanner toy, and is currently a unique feature on the Samsung Galaxy Note 7. It’s far more secure than fingerprint scanning, but early reports indicate that it’s slower and more inconvenient. Even so, thieves will have a hard time replicating your iris in order to access your data so iris scanning might be your best option.
3. Smartphone technology

You can put your phone in Airplane Mode or you can hold the power button and turn it off. However, Edward Snowden rightly believes that malware can be installed on your device to simulate those features while still reporting your location. The only way to be sure your phone isn’t talking to the wrong people is to yank the battery.
Phones like new LG G5 are doing some things to work around that. The flagship smartphone was redesigned to take advantage of LG Friends products, which are modular accessories that add special features to your phone. The accessories haven’t really taken off, but it gives the G5 the unique ability to pop the battery out with the push of a button. It also has a fingerprint reader and the newest Android with encrypted data protection built in.
When it’s turned off you can’t use the camera, microphone, or notepad features that make a smartphone so useful when acting covertly. You’ll have to check how safe you are, then with a quick pop the battery is back in and you can get recording.
4.Encrypted Instant Messenger

There are dozens, maybe hundreds of Instant Messaging apps out there. We all have our favorite, and our friends have theirs (which we have too just to use just to stay in contact). If you want to be sure that only you and your recipient will be able to read your conversation, you need to use Signal (available for iOS and Android).
Once you install it, the app checks your contacts and immediately connects you to anyone else who has the app installed. There are no animated stickers here. The design is minimal and fits right in with Android or iOS’s design specs.
If your friends are unwilling to part with their IM app-of-choice, you have to do your research. WhatsApp supports encryption using the same algorithm used in Signal, but they were acquired by Facebook in 2014 and that makes some users uncomfortable. Google’s forthcoming Allo app will replace Hangouts, but only enables end-to-end encryption with Incognito Mode conversations and are deleted when the conversation ends. Apple’s iMessage and FaceTime both support end-to-end encryption as well. Just make sure to encrypt your backups because all your conversations will wind up there.
5. Anti-Virus Software
No sooner than someone says an operating system is virus-proof than someone tries to write a virus for it. While not the plague it was for desktop computers in the 90s, viruses are still a very real possibility even if you only download from the official Apple or Google app stores.
To that end, there are several anti-virus apps that sit in the background and scan every app that comes through the doors. Lookout Security & Antivirus is one of the grandaddies on the mobile platform. It’s available on Android and iOS for free and remains one of the highest ranked antivirus apps. Additional features are unlocked for $2.99 a month or $29.99 annually.
6. Password Safes
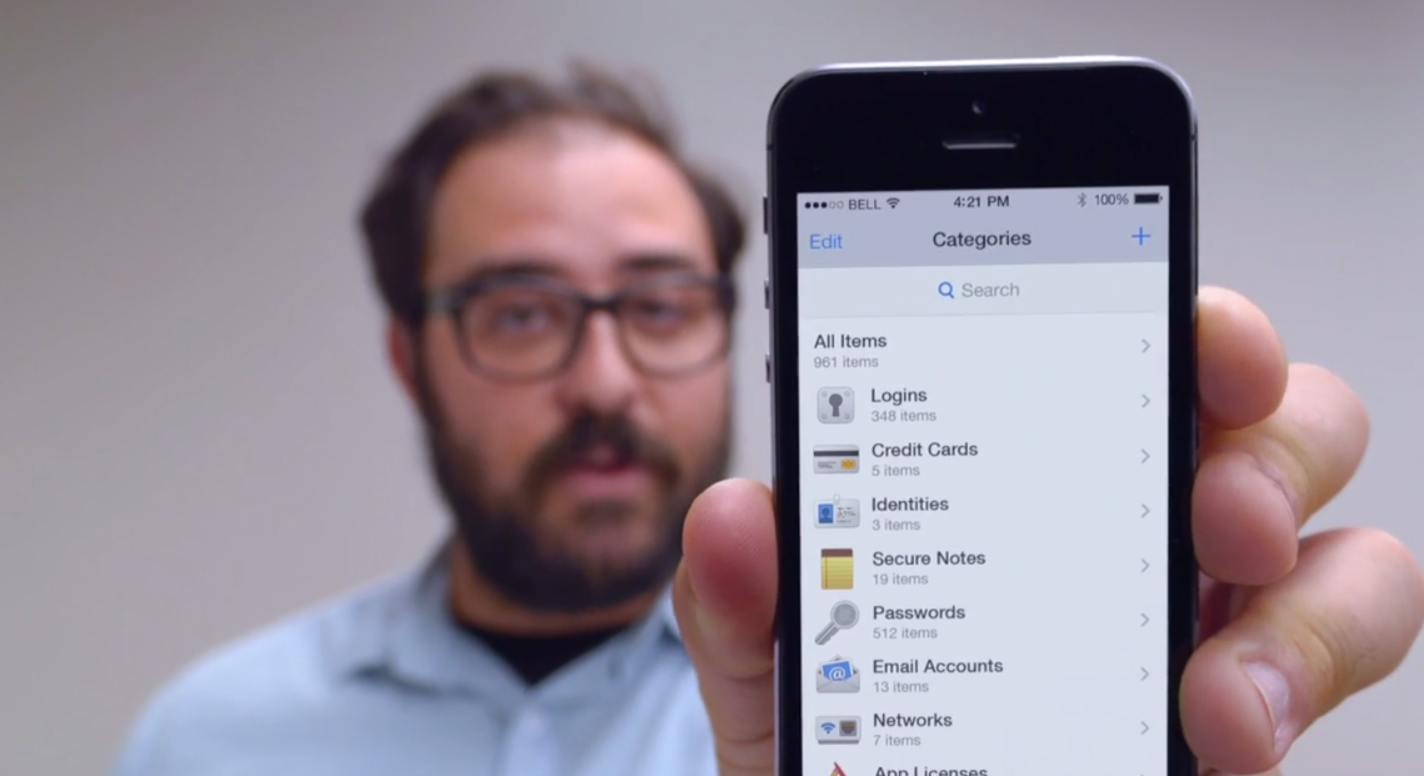
Thinking up a new password for every email address, e-card site, and cat video portal is exhausting. Eventually, you start to recycle passwords. It then only takes one hacked Sony or LinkedIn to expose your accounts on every site where that password is used. Password managers like 1Password and LastPass securely store your passwords, and release them only when authorized by a master password or fingerprint reader.
While they can store your weakly generated and repeated passwords, password safes can also randomize unique passwords for each site. Securely storing ‘passw0rd123’ is good, but no hacker will guess a 16-digit random collection of letters and numbers. Since they will automatically populate username and password fields in your browser or apps, you’ll never need to type it in either. Both 1Password and LastPass can be installed on your desktop browsers so you have full access to those secure sites everywhere.
7. DTEK by Blackberry
You’ve set a secure password on your lock screen, you’ve turned off Google’s tracking, you disable WiFi when outside the house, but there’s still lots of work to do. Just one year ago privacy experts found that simply having Uber installed on your phone could send buckets of your data to their servers, even if you weren’t using the app.
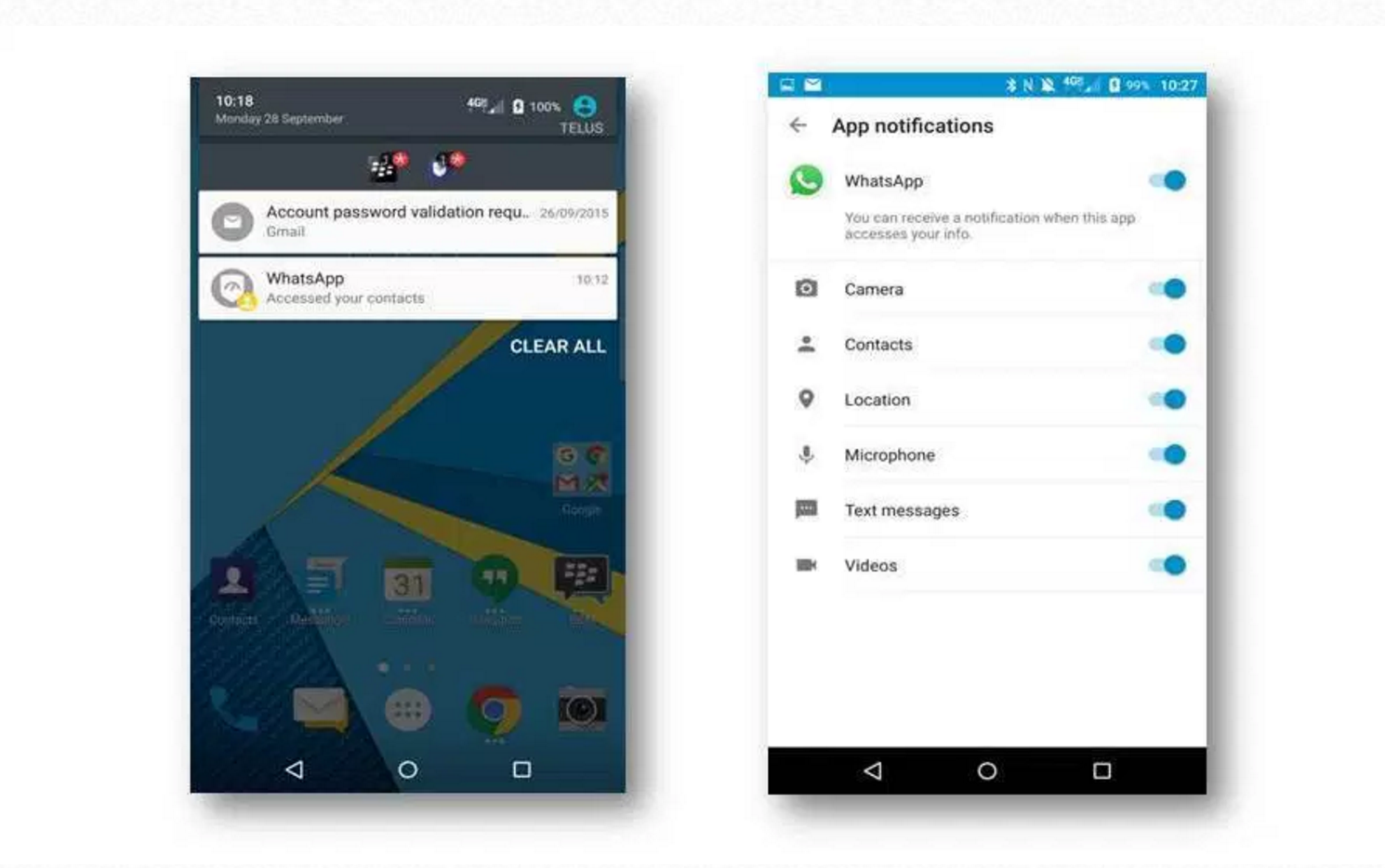
Enter DTEK by Blackberry. It will scan all potential security breaches on your phone. If an app decides to turn on your microphone, DTEK flashes you a warning. Most of the time it will probably be okay, but that one time it’s not you’ll appreciate the warning.
DTEK keeps a log of the access each app receives and reports back to you how many times it has, for example, read your contacts. It even has Factory Reset Protection, which stops thieves from wiping your device to prevent you from tracking it. All this security sounds like a lot of work, but that’s the beautiful thing about DTEK. The clean interface makes it all very simple for the casual user.
Sadly, the DTEK app requires deep access to the phone’s OS. That’s only possible for Blackberry on their own devices; the Blackberry PRIV and DTEK50. Both are Android phones with hardware features comparable to other high-end and mid-range Android flagships. If Blackberry decides at the end of the year to get out of the hardware game, the DTEK software may be opened to other devices.
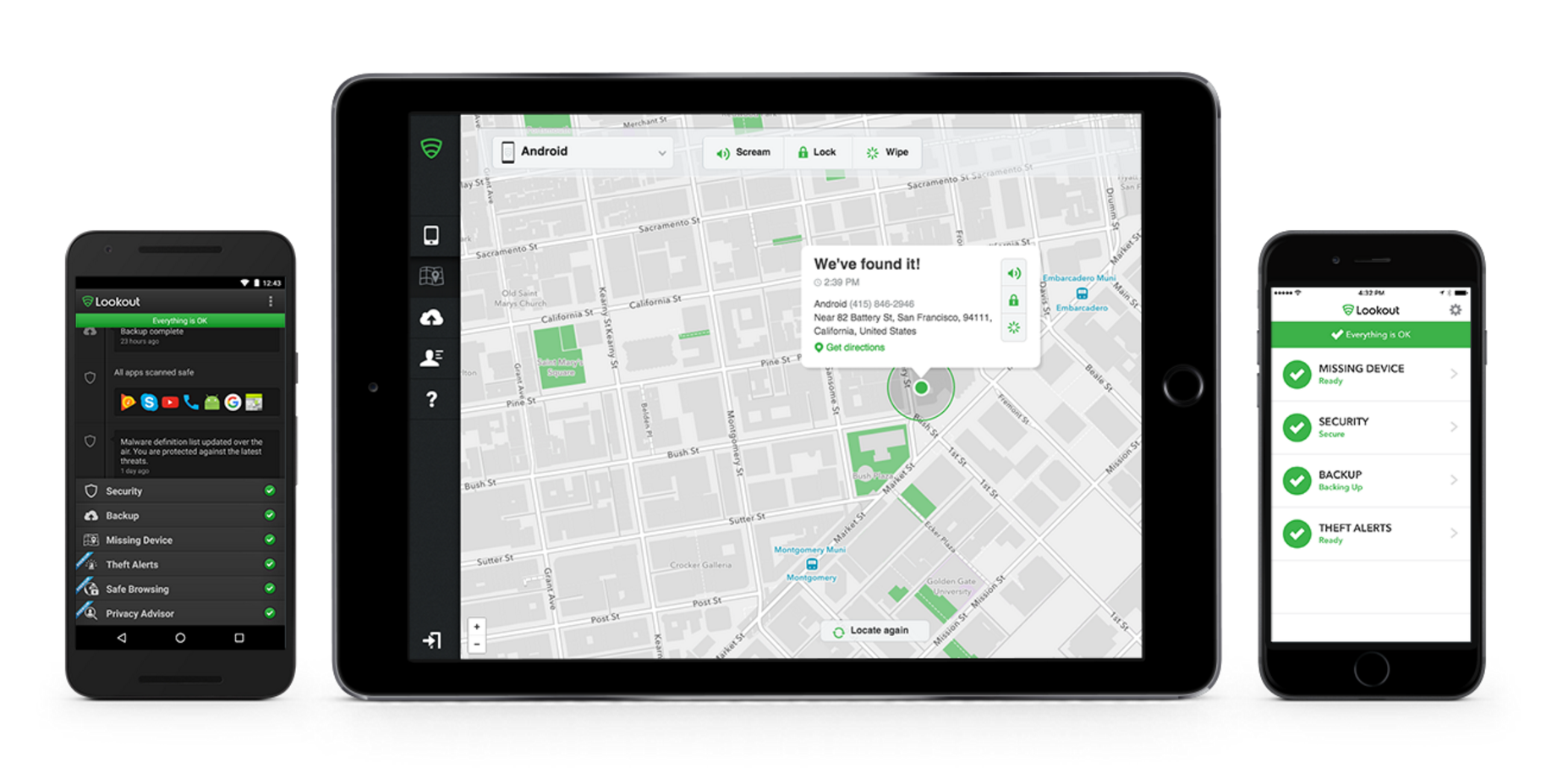
8. Tracking software
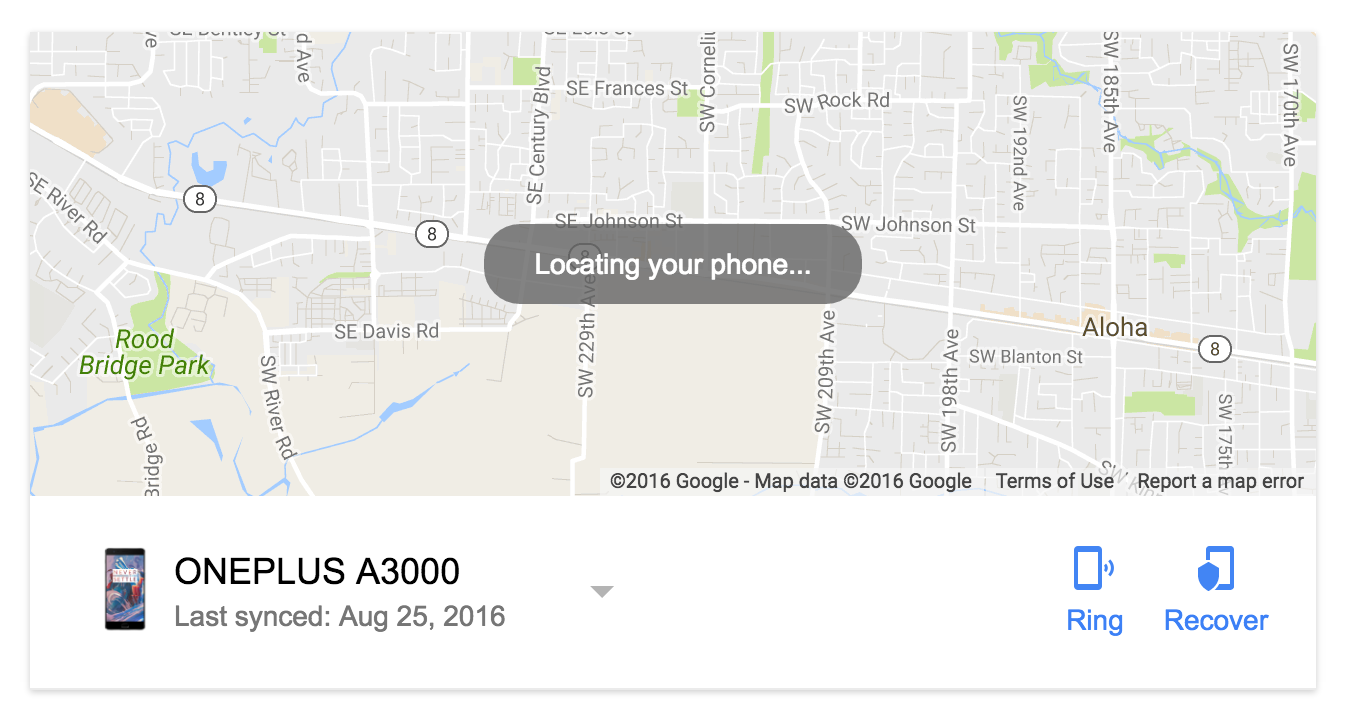
Sometimes, tracking your phone is a good thing. Your phone goes missing, and all your photos, notes and interview recordings are on there.
For at least a few years, both iOS and Android have had tracking software built into your phones in case they get lost or stolen. Using iCloud.com (link), iPhone users can locate their device, lock the screen, lock the activation (so it can’t be resold and reactivated), or remotely wipe the device clean.
When logged into your Google account, a simple search engine query of “Find my phone” will bring up a map for any of your registered devices. From the web-based interface you can force it to ring (even if the sound is off). Useful for when you just can’t find it around house, or when you know the thief is nearby and you want it to send up a flare. From here you can also reset the password, or completely lock out the device.
9. VPN
A Virtual Private Network sits between you and the Internet. It’s like a butler that goes out, gets the newspaper, and returns without anyone knowing you like reading supermarket tabloids. VPNs can be used to keep your information anonymous when visiting web sites, place you in different countries (so you can watch Netflix’s BBC lineup), and most importantly, encrypt your data transfer.
Avoid free VPNs. If you don’t know how they’re making money, then they might be making money on you. Spring the few bucks a month it takes to secure all your connections in and out of your smartphone with a service like NordVPN. Is one level of encryption not good enough? NordVPN offers Double VPN which runs AES-256-CBC encryption on your data transfers two times at the expense of some speed. The feature is optional and can be enabled for those times when you’re feeling as paranoid as Edward Snowden. The service is $8 per month, or $69 for the year.
 Keep scrolling for more great stories.
Keep scrolling for more great stories.
