The NSA’s Most Powerful Cyberweapons Are Being Used Against Us
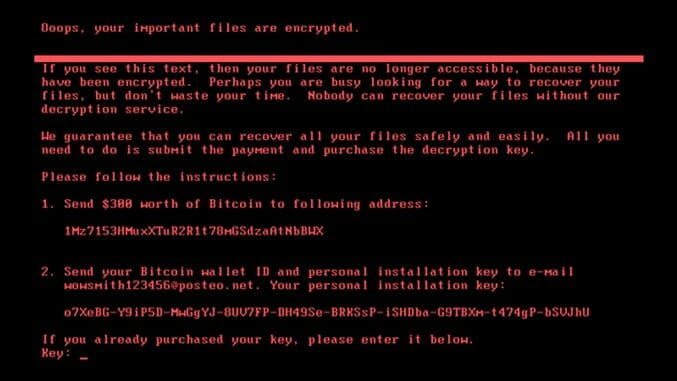
Welcome to the new age of cyber warfare. The image you see above was born in the NSA, and has now made its way out to the masses by virtue of the U.S. military’s ineptitude. As a result, the weapon has now been turned against us.
Symantec confirms global #Petya ransomware attack hitting computers today (hospitals, supermarkets, banks) uses NSA’s #ETERNALBLUE exploit. pic.twitter.com/wDuHoRcFCr
— Edward Snowden (@Snowden) June 27, 2017
Petya on an ATM. Photo by REUTERS.https://t.co/fDQ0nGyQc6pic.twitter.com/gT2xQP9wAo
— Mikko Hypponen (@mikko) June 27, 2017
Vice Prime Minister of Ukraine, ????? ??????? (Pavlo Rozenko) on Facebook. This is what Petya looks like when it’s encrypting your drive. pic.twitter.com/RgPtfuWK7p
— Mikko Hypponen (@mikko) June 27, 2017
I’m hearing a nuclear power plant industrial network is infected with Petya.
— Kevin Beaumont (@GossiTheDog) June 27, 2017
If machine reboots and you see this message, power off immediately! This is the encryption process. If you do not power on, files are fine. pic.twitter.com/IqwzWdlrX6
— Hacker Fantastic (@hackerfantastic) June 27, 2017
Yesterday, one of the largest cyber-attacks in history hit Ukraine and then quickly spread across the globe. Per CNET:
The new ransomware, identified by security firm Bitdefender as GoldenEye, has two layers of encryption, researchers said. It locks up both your files and your computer’s file system.
“Just like Petya, it is particularly dangerous because it doesn’t only encrypt files, it also encrypts the hard drive as well,” said Bogdan Botezatu, a senior threat analyst with Bitdefender.
This is a similar attack from the one last month, which starred the WanaCry ransomware that shut down entire hospitals in the United Kingdom.
I am on a train analysing Petya. I think this will be bigger than WannaCry. It’s much better designed. Has automated lateral movement.
— Kevin Beaumont (@GossiTheDog) June 27, 2017
According to legendary information security researcher, the grugq, the “ransom” part of the ransomware in yesterday’s attack was poorly designed.
Although the worm is camouflaged to look like the infamous Petya ransomware, it has an extremely poor payment pipeline. There is a single hardcoded BTC wallet and the instructions require sending an email with a large amount of complex strings (something that a novice computer victim is unlikely to get right.)
Predictably, within hours the email address had been disabled by the service provider. If this well engineered and highly crafted worm was meant to generate revenue, this payment pipeline was possibly the worst of all options (short of “send a personal cheque to: Petya Payments, PO Box …”)
Correct. They modelled it after Petya but it’s not actually Petya. I doubt intent was actually ransomware, too easy to close email acct. https://t.co/lBZlVFrbTX
— Kevin Beaumont (@GossiTheDog) June 27, 2017
Matt Suiche, founder of the cybersecurity firm Comae, wrote in a blog post titled “Petya.2017 is a wiper not a ransomware:”
TL;DR: The ransomware was a lure for the media, this version of Petya actually wipes the first sectors of the disk like we have seen with malwares such as Shamoon.
Britain’s National Cyber Security Centre and the NSA both blamed the WannaCry attack on Lazarus Group, a hacker collective. Not much is known about the group, but it is supposedly tied to North Korea. When the United States government attributed the infamous Sony hack (where Seth Rogen and James Franco’s comedy about North Korea was leaked) to the North Korean government, they really meant Lazarus Group. Yesterday’s attack has not been attributed to anyone yet, but the tools used have been proven to reside in their hands. However, Lazarus Group is certainly not the only one with access to some of the world’s most potent cyber weapons.
So how did we get here?
In short: The Shadow Brokers. Wikipedia provides a pretty good tl;dr explanation of who they are and why you should care at the very top of their page:
The Shadow Brokers (TSB) is a hacker group who first appeared in the summer of 2016. They published several leaks containing hacking tools from the National Security Agency (NSA), including several zero-day exploits. Specifically, these exploits and vulnerabilities targeted enterprise firewalls, anti-virus products, and Microsoft products.
Zero-day exploits are bad. Like digital weapons of mass destruction bad. That NSA hack they reference? That was a big freaking deal that the media made a big freaking deal for about four hours before going back to chase the Trump-shaped rabbit circling around the track. The Shadow Brokers leaked/are leaking portions of their hack at a time, as Ars Technica wrote about TSB’s latest dump on April 14th (emphasis mine):
“It is by far the most powerful cache of exploits ever released,” Matthew Hickey, a security expert and co-founder of Hacker House, told Ars. “It is very significant as it effectively puts cyber weapons in the hands of anyone who downloads it. A number of these attacks appear to be 0-day exploits which have no patch and work completely from a remote network perspective.”
One of the Windows zero-days flagged by Hickey is dubbed Eternalblue. It exploits a remote code-execution bug in the latest version of Windows 2008 R2 using the server message block and NetBT protocols.
From CNET detailing yesterday’s attack (emphasis mine):
Researchers from Symantec confirmed that the GoldenEye ransomware used EternalBlue, the NSA exploit that fueled WannaCry’s spread. So far, more than $4,600 has been paid to the attackers’ bitcoin wallet in 19 payments.
Ukrainian police confirm that tax software MeDoc was initial ransomware attack vector https://t.co/4KeyYrecsu
— Eric Geller (@ericgeller) June 27, 2017
After the WannaCry attack, TSB posted on their blog in their usual mangled English:
Q. What is being difference between ransom and sale?
A. Sale is buy or no buy, no bad things happen if no buy. Ransom is buy or bad things happen to you. Yes?
TheShadowBrokers is feeling like being very responsible party about Windows dump. Do thepeoples be preferring theshadowbrokers dump windows in January or August? No warning, no time to patch? this is being theshadowbrokers version of alternative facts.
In August theshadowbrokers is telling thepeoples theequationgroup fails at security, theequationgroup is losing their data. Is telling thepeoples, theshadowbrokers is having equation group data, hacker tools for auctioning. Auctioning is sale, bid or no bid. Auction is not ransom. TheShadowBrokers is releasing theequationgroup 2013 firewall tools as proof and advertising. Only Zero-Day is old Cisco.
Before you begin envisioning these hackers as a collective of unbeatable digital savants, this passage from their latest post is instructive:
Is theshadowbrokers doing correct? If not theshadowbrokers is sure many haters be posting smart comments. Is being ok, theshadowbrokers fucks your moms. You getting idea.
The long of this tale is that the NSA got hacked and now its own offensive cyberweapons are being turned on the citizens of the world. The 1965 equivalent to what we are currently enduring is if any schmuck could show up to a Raytheon auction and walk away with an intercontinental ballistic missile. This is pandora’s box being pursued to its logical ends.
Pre-ransomware advice:
BackupPatch
– Turn off unneeded featuresPost-ransomware advice:
BackupPatch
– Turn off unneeded features— matt blaze (@mattblaze) May 13, 2017
Stuxnet is the cyberweapon that most people have heard of—thanks to the victory lap it took in American media after it damaged physical infrastructure in Iranian nuclear facilities—but it was not the first. George W. Bush’s Iraq War served as the staging ground for the initial cyber offensives. From attacking cell phones and computers used to blow up roadside bombs, to hacking some of the most vicious terrorists al-Qaeda in Iraq had to offer and luring them into a trap, the United States demonstrated a vast array of cyber capabilities that when used in tandem with kinetic warfare, were quite deadly.
Once the United States began the era of Cyber War, it was inevitable that others would follow. It’s common knowledge that China has hacked this country literally to its core, and most of what Edward Snowden took from the NSA was already known by Russian hackers (with a huge assist from Jeffrey Delisle, a former sub-lieutenant in the Royal Canadian Navy who passed reams of information to Russian Military Intelligence six years before anyone had heard Edward Snowden’s name). Non-state actors soon emerged as major players in this space to bring a whole new angle to this odd world of diplomacy. It’s impossible for any layman to truly know where collectives like Lazarus Group and The Shadow Brokers allegiance’s lie, and given the subculture of hacking, it’s very possible that they’re just doing this for the lulz.
One thing that is for certain: this is the result of a bloated cyber security state that has been subsumed into the military industrial complex. Much has been made of millennial leakers like Edward Snowden and Reality Winner, but the reality of the situation is that if the military didn’t depend on contractors as heavily as it does, it would be easier to resolve this stuff in-house. It’s their own largesse and sloppiness that led to putting classified information in the hands of inexperienced people willing to take it public, and it’s that same largesse and sloppiness that has now endangered the entire globe, as faceless collectives are conducting an all-out assault on the citizens of the world with stolen cyber superweapons—and it’s unlikely to get better any time soon, as the head of the French military’s digital crime unit, Nicolas Duvinage told AFP “this is a bit like a flu epidemic in winter. We will get many of these viral attack waves in coming months.”
Jacob Weindling is a staff writer for Paste politics. Follow him on Twitter at @Jakeweindling.